The sys admin's daily grind: UFW
Lack of Defense

Things were better back then. No way! Charly takes a look back at the bad old firewall days and explains why things are better today – assuming you have the right tools.
Watch out, Granddaddy Charly is about to tell his old war stories again: We had nothing back then. If you were in firewall support, that meant working on the front, in your underwear, at temperatures of minus 20 degrees. And, we used to have to build firewall rulesets using BSD's built-in IPFW tool, which didn't even have stateful packet inspection at the time. People kept locking themselves out of the command center or shooting themselves in the foot.
IPWF led to ipchains, which was a blessing; it was followed in kernel 2.4 by iptables, on which most of today's Linux firewalls are based – although the designated successor, nftables, went missing in action some time ago.
However, you can't teach the troops iptables in five minutes – not even the basic routines, such as allow all outgoing, block all incoming, except for connections on ports 22, 80, and 443. Uncomplicated Firewall [1], UFW is actually a much better choice for building just-so firewalls.
Originally developed for Ubuntu, UFW is now included with most Debian-based distributions and Arch Linux. If you built your house on some other underpinnings, you can still download the tarball [1] and run the usual installer suspects.
You just need two commands to set the default rules:
sudo ufw default deny incoming sudo ufw default allow outgoing
The following allows external access to the SSH and web services:
sudo ufw allow ssh sudo ufw allow http sudo ufw allow https
The service names are as defined in /etc/services. Of course, this would work with the port numbers, too (i.e., with 22/tcp instead of ssh).
Service Is Service, Normally
Using sudo ufw enable enables the rules, and you can check this by typing sudo ufw status verbose. But, what if you use Mosh instead of SSH? Mosh needs access to UDP ports 60000 through 61000. You can handle this in UFW with the following command:
sudo ufw allow 60000:61000/udp
UFW, however, offers an even easier approach. It comes with shortcuts for individual services; you can type ufw app list to list them. To my delight, my buddy Mosh is on the list. To give Mosh the run of the root, I just type:
sudo ufw allow mosh
Just to check, I type sudo ufw status verbose again; you can see the results in Figure 1. UFW has enabled all the rules for both IPv4 and IPv6; good thinking! You can manage this behavior in the /etc/default/ufw file's IPV6 = Yes line. Additionally, if you want to remove a rule on the fly, you can do so with the delete keyword, as in:
sudo ufw delete allow mosh
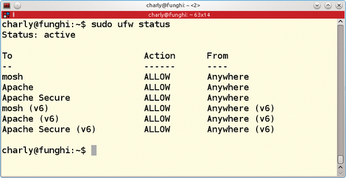 Figure 1: After a few lines of configuration, the UFW firewall already gives me some protection against attacks.
Figure 1: After a few lines of configuration, the UFW firewall already gives me some protection against attacks.
Granddaddy Charly would have really appreciated this kind of defense back when he was manning a rusty old IPFW bazooka.
Infos
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Red Hat Adds New Deployment Option for Enterprise Linux Platforms
Red Hat has re-imagined enterprise Linux for an AI future with Image Mode.
-
OSJH and LPI Release 2024 Open Source Pros Job Survey Results
See what open source professionals look for in a new role.
-
Proton 9.0-1 Released to Improve Gaming with Steam
The latest release of Proton 9 adds several improvements and fixes an issue that has been problematic for Linux users.
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.

