Using Sudo Options to Enhance Security
Sudo Security Voodoo
ByBy taking the time to learn sudo's many options, you can make your system more secure with a little creativity.
Thanks to Ubuntu, sudo is best known as a quick way to run commands as root. However, there’s far more to sudo than Ubuntu’s policy. In fact, sudo’s man page is over 2,400 lines long, covering a staggering number of situations -- some of which, like many powerful Linux commands, can get you in a lot of trouble if you are careless. Among sudo’s options are many that can greatly enhance security, especially if you take the time to be creative.
Why would you want to enhance your security? The answer is that, from a security viewpoint, Ubuntu’s use of sudo can be viewed as a problem (although opinions do differ). As you may know, when sudo is configured the way it is in Ubuntu, you can use the password for your everyday account to log in to sudo and run root commands. The trouble is that any password for an everyday account is exposed in a way that the root account is not, especially on the Internet. That means that if the everyday account is compromised, the intruder gains root access, too, if sudo is set up on the system. The traditional separate root password is more secure, although less convenient. Fortunately, though, you can manage both convenience and security by taking the time to learn the details of sudo.
Editing sudoers
sudo has a unique configuration system. Like many configuration files, sudo’s behavior is set by a file in the /etc/directory. sudo’s configuration file is sudoers (Figure 1), which lists default behaviors and the privileges granted to individual users. As the top of the sudoers file warns, it should only be edited using the visudo command. visudo is designed to prevent you from editing sudoers in a way that would cripple or disable sudo by doing all editing in a temporary file and replacing the original file only when all editing is done. Should you make an error while editing sudoers, as you try to save, visudo will give you the option to reopen its temporary copy of sudoers to correct the errors (e) or discard your edits (X) -- choices that you obviously should not ignore. Depending on the distribution, visudo may or may not display these choices, but they will be available whether displayed or not.
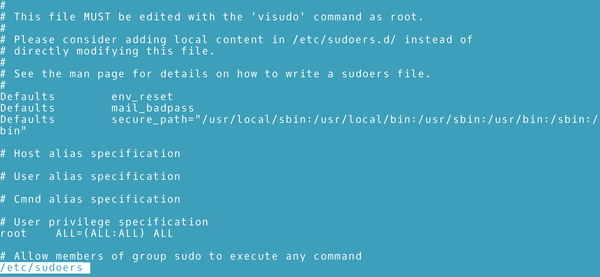 Figure 1: The sudo configuration file, sudoers, lists the default behaviors and privileges for users.
Figure 1: The sudo configuration file, sudoers, lists the default behaviors and privileges for users.
Starting visudo opens a command-line text editor. Usually, this editor is Vim, but you can also set another editor. For instance, if you want visudo to open nano instead, you can change the environmental variable with the command:
export VISUAL=nano; visudo
The sudoers file itself is divided into three sections. The first section is the default behaviors. It lists one option per line. For example, if you want to use the insults option -- a genuine option, which insults users who make mistakes trying to log in to sudo -- the entry is:
Defaults insult
Default settings can be overridden by specific users' or groups' settings. However, above the specific settings is a section that defines aliases for hosts (host names, IP addresses, network numbers, or netgroups), for users (account names, UIDs, groups or netgroups), for users to run as (account names, UIDs, groups or netgroups), and for commands (usually with full path names). All aliases consist of uppercase characters or underscores.
These aliases exist to make the defining of specific settings less cumbersome. For example, if you want user accounts bab, plw, and vaf to all have the same privileges, you could create the alias
User_Alias ADMIN = bab,plw,vaf
With this user alias defined, you can simply defined privileges for ADMIN, instead of for bab, plw, and vaf separately. In the same way, you create an alias for a list of network terminals from which a sudo user can log in or a set of commands that a group can or cannot use. Although aliases can take time to set up, they make creating a new set of privileges or editing an old set much easier.
In the third section, individual privileges are defined one per line, using this structure:
[USER or ALIAS] [TERMINALS]=[USER RUN AS] [OPTIONS:] [PERMISSIONS]
Permissions are generally those that a user or alias can use, but adding an exclamation mark (!) in front of them turns the list into those that cannot be used.
For instance, the basic entry for the root user with all privileges is:
root ALL=(ALL) ALL
Individual terminals or commands can be entered instead of ALL. USER RUN AS and OPTIONS are optional, so that the line
bab ALL= (ROOT) passwd, chown, chgrp, chmod
is enough to give user bab the ability to change passwords and permissions from all terminals on the system, while running as root. More simply still, defining an alias called ATTRIBUTES that included all four commands would reduce the line to:
bb ALL=(ROOT) PERMISSIONS
Remember, though, that specific permissions override those set as defaults.
Defaults, Privileges, and Options
Defaults and privileges are defined using the options listed in the sudoers man page. The available options range from requiring no login whatsoever to specific settings for greater security.
Many security options affect how to log in to sudo. For example, password_tries=NUMBER sets how many times a user can try to log in before being denied. It is accompanied by passwd_timeout= MINUTES, which sets how long sudo runs before logging out a user -- an especially useful feature when using root privileges, since basic security decrees that the root account should be used for as short a time as possible. With passwd_timeout, you no long have to rely on your own memory to close root as soon as possible. Less drastically, timestamp_timeout=MINUTES sets the time before sudo prompts for another login.
Other options set which password sudo requires from you. The option runaspw requires the current account’s password, just as in Ubuntu. However, you can do better than that simply by specifying rootpw, which requires the root password. Subtler still, targetpw USER can require another account's password , so that you set up a user with root privileges that is used only with sudo. With targetpw, an intruder will need to be able to read the list of users in order to find the password for sudo.
Still another basic piece of security is noexec. noexec is designed to limit the running of applications from which other commands can be run. Without noexec, the running of one application could easily give intruders access to other applications in the system.
However, individual privileges are where ingenuity reigns. With a little planning, you could set up separate accounts with limited root privileges. For example, one account could only be permitted to run tools for installing package managers, such as Debian’s apt-get, apt, and dpkg, while another would be limited to running commands for changing file attributes. With such an arrangement, Linux can be made to mimic other sophisticated Unix descendants. While each limited account can do specific functions, an intruder who gains access to one account via sudo would not have complete control over the system.
Getting More from Sudo
sudo is a sophisticated command. However, as you can see, it is also a seriously under-used one. Even if you have no interest in such options as setting the command prompt, there are still a number of options that can make switching into sudo to temporarily gain root privileges safer -- and all without sacrificing any convenience once everything is configured.
It is easy to think of sudo as a magical word that some distributions require at the front of administrative commands. And for many people, that may be enough. But sudo can also be much more. You might even investigate sudo plugins like Privilege Manager for Sudo, which allows you to set policies for sudo graphically, or sudo_pair, which requires an admin to approve any use of sudo.
But, one way or the other, if you are concerned about security, you owe yourself the time to learn what else sudo can do.
next page » 1 2
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
OpenMandriva Lx 6.0 Available for Installation
The latest release of OpenMandriva has arrived with a new kernel, an updated Plasma desktop, and a server edition.
-
TrueNAS 25.04 Arrives with Thousands of Changes
One of the most popular Linux-based NAS solutions has rolled out the latest edition, based on Ubuntu 25.04.
-
Fedora 42 Available with Two New Spins
The latest release from the Fedora Project includes the usual updates, a new kernel, an official KDE Plasma spin, and a new System76 spin.
-
So Long, ArcoLinux
The ArcoLinux distribution is the latest Linux distribution to shut down.
-
What Open Source Pros Look for in a Job Role
Learn what professionals in technical and non-technical roles say is most important when seeking a new position.
-
Asahi Linux Runs into Issues with M4 Support
Due to Apple Silicon changes, the Asahi Linux project is at odds with adding support for the M4 chips.
-
Plasma 6.3.4 Now Available
Although not a major release, Plasma 6.3.4 does fix some bugs and offer a subtle change for the Plasma sidebar.
-
Linux Kernel 6.15 First Release Candidate Now Available
Linux Torvalds has announced that the release candidate for the final release of the Linux 6.15 series is now available.
-
Akamai Will Host kernel.org
The organization dedicated to cloud-based solutions has agreed to host kernel.org to deliver long-term stability for the development team.
-
Linux Kernel 6.14 Released
The latest Linux kernel has arrived with extra Rust support and more.
