Features
Keeping Secrets
Encryption with VeraCrypt
Protect your data and operating system from prying eyes with VeraCrypt.
Hunting and Gathering
Researching a target with passive reconnaissance tools
Cyberattacks often start with preliminary research on network assets and the people who use them. We'll show you some of the tools attackers use to get information.
Keys, shells, and layouts – find the right keyboard for your needs
What to Look for in an Ergonomic Keyboard
Today there are increasing options for keyboards better suited to long days spent at a desk, including options for customization.
Choices
Choosing an open source database management system
Open source database management systems offer greater flexibility and lower costs while avoiding vendor lock-in. Finding the right one depends on your project's needs.
Domains Gone Astray
Preventing DNS subdomain hijacking
Attackers can use poorly maintained DNS records to gain access to your IP address. The open source DNS Reaper lets you monitor your records to ward off attacks.
Get Organized
Scheduling tools for Linux
If you need help staying organized, Linux does not let you down with its large collection of organization and scheduling tools.
Snake Charmer
Using Python in the browser
PyScript lets you use your favorite Python libraries on client-side web pages.
ELevate to the Future
Migrating from CentOS 7
CentOS 7 reaches end of life in June 2024, forcing users to look for a free enterprise Linux alternative. AlmaLinux's ELevate migration tool can help ease the transition.
Keyboardio: Waiting for Chrysalis
A Graphical Interface for Customizing Keyboard Layouts
How is the popular keyboard manufacturer's graphical installer after nine years in development?
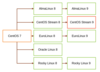
Together
Bonding your network adapters for better performance
Combining your network adapters can speed up network performance – but a little more testing could lead to better choices.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.